simple-casbin
v1.1.6
Published
An authorization library that supports access control models like ACL, RBAC, ABAC in Node.JS
Downloads
4
Readme
simple-casbin
News: still worry about how to write the correct node-Casbin policy? Casbin online editor is coming to help! Try it at: http://casbin.org/editor/

simple-casbin is a powerful and efficient open-source access control library for NodeJS and Browser Envirorment. It provides support for enforcing authorization based on various access control models.
All the languages supported by Casbin:
 |
|  |
|  |
|  ----|----|----|----
Casbin | jCasbin | node-Casbin | PHP-Casbin
production-ready | production-ready | production-ready | production-ready
----|----|----|----
Casbin | jCasbin | node-Casbin | PHP-Casbin
production-ready | production-ready | production-ready | production-ready
Installation
npm install simple-casbin --saveGet started
Initialize a new simple-Casbin enforcer with a model file and a policy file:
const enforcer = await new Enforcer(fs.readFileSync('model.conf', {encoding: 'utf-8'}), new FileAdapter(policyPath)); // or from a empty model const enforcer = await new Enforcer(new Model(), new FileAdapter(policyPath));Note: you can also initialize an enforcer with policy in DB instead of file, see Persistence section for details.
Add an enforcement hook into your code right before the access happens:
const sub = 'alice'; // the user that wants to access a resource. const obj = 'data1'; // the resource that is going to be accessed. const act = 'read'; // the operation that the user performs on the resource. if (enforcer.enforce(sub, obj, act) == true) { // permit alice to read data1 } else { // deny the request, show an error }Besides the static policy file, node-Casbin also provides API for permission management at run-time. For example, You can get all the roles assigned to a user as below:
const roles = enforcer.getRoles('alice');See Policy management APIs for more usage.
Please refer to the src/test package for more usage.
Table of contents
- Supported models
- How it works?
- Features
- Documentation
- Online editor
- Tutorials
- Policy management
- Policy persistence
- Role manager
- Examples
- Our adopters
Supported models
- ACL (Access Control List)
- ACL with superuser
- ACL without users: especially useful for systems that don't have authentication or user log-ins.
- ACL without resources: some scenarios may target for a type of resources instead of an individual resource by using permissions like
write-article,read-log. It doesn't control the access to a specific article or log. - RBAC (Role-Based Access Control)
- RBAC with resource roles: both users and resources can have roles (or groups) at the same time.
- RBAC with domains/tenants: users can have different role sets for different domains/tenants.
- ABAC (Attribute-Based Access Control): syntax sugar like
resource.Ownercan be used to get the attribute for a resource. - RESTful: supports paths like
/res/*,/res/:idand HTTP methods likeGET,POST,PUT,DELETE. - Deny-override: both allow and deny authorizations are supported, deny overrides the allow.
- Priority: the policy rules can be prioritized like firewall rules.
How it works?
In node-Casbin, an access control model is abstracted into a CONF file based on the PERM metamodel (Policy, Effect, Request, Matchers). So switching or upgrading the authorization mechanism for a project is just as simple as modifying a configuration. You can customize your own access control model by combining the available models. For example, you can get RBAC roles and ABAC attributes together inside one model and share one set of policy rules.
The most basic and simplest model in node-Casbin is ACL. ACL's model CONF is:
# Request definition
[request_definition]
r = sub, obj, act
# Policy definition
[policy_definition]
p = sub, obj, act
# Policy effect
[policy_effect]
e = some(where (p.eft == allow))
# Matchers
[matchers]
m = r.sub == p.sub && r.obj == p.obj && r.act == p.actAn example policy for ACL model is like:
p, alice, data1, read
p, bob, data2, writeIt means:
- alice can read data1
- bob can write data2
Features
What node-Casbin does:
- enforce the policy in the classic
{subject, object, action}form or a customized form as you defined, both allow and deny authorizations are supported. - handle the storage of the access control model and its policy.
- manage the role-user mappings and role-role mappings (aka role hierarchy in RBAC).
- support built-in superuser like
rootoradministrator. A superuser can do anything without explict permissions. - multiple built-in operators to support the rule matching. For example,
keyMatchcan map a resource key/foo/barto the pattern/foo*.
What node-Casbin does NOT do:
- authentication (aka verify
usernameandpasswordwhen a user logs in) - manage the list of users or roles. I believe it's more convenient for the project itself to manage these entities. Users usually have their passwords, and node-Casbin is not designed as a password container. However, node-Casbin stores the user-role mapping for the RBAC scenario.
Documentation
https://casbin.org/docs/en/overview
Online editor
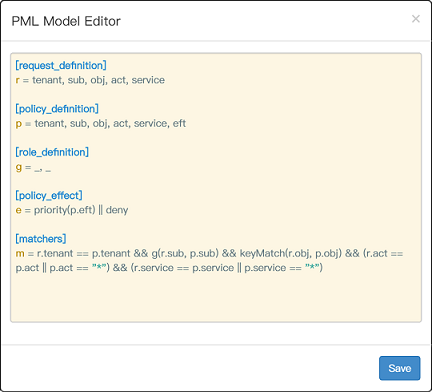
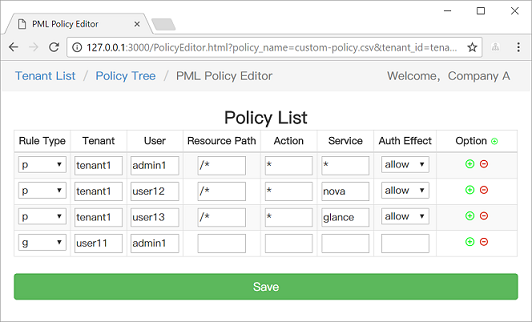
You can also use the online editor (http://casbin.org/editor/) to write your node-Casbin model and policy in your web browser. It provides functionality such as syntax highlighting and code completion, just like an IDE for a programming language.
Tutorials
https://casbin.org/docs/en/tutorials
Policy management
node-Casbin provides two sets of APIs to manage permissions:
- Management API: the primitive API that provides full support for node-Casbin policy management.
- RBAC API: a more friendly API for RBAC. This API is a subset of Management API. The RBAC users could use this API to simplify the code.
We also provide a web-based UI for model management and policy management:
Policy persistence
In node-Casbin, the policy storage is implemented as an adapter (aka middleware for node-Casbin). To keep light-weight, we don't put adapter code in the main library (except the default file adapter). A complete list of node-Casbin adapters is provided as below. Any 3rd-party contribution on a new adapter is welcomed, please inform us and I will put it in this list:)
Adapter | Type | Author | Description ----|------|----|---- File Adapter (built-in) | File | node-Casbin | Persistence for .CSV (Comma-Separated Values) files Sequelize Adapter | ORM | node-Casbin | MySQL, PostgreSQL, SQLite, Microsoft SQL Server are supported by Sequelize Waterline Adapter | ORM | node-Casbin | MySQL, MongoDB, neDB, Postgres are supported by Waterline TypeORM Adapter | ORM | node-Casbin | MySQL, PostgreSQL, MariaDB, SQLite, MS SQL Server, Oracle, WebSQL, MongoDB are supported by TypeORM
For details of adapters, please refer to the documentation: https://github.com/casbin/casbin/wiki/Policy-persistence
Role manager
The role manager is used to manage the RBAC role hierarchy (user-role mapping) in node-Casbin. A role manager can retrieve the role data from node-Casbin policy rules or external sources such as LDAP, Okta, Auth0, Azure AD, etc. We support different implementations of a role manager. To keep light-weight, we don't put role manager code in the main library (except the default role manager). A complete list of node-Casbin role managers is provided as below. Any 3rd-party contribution on a new role manager is welcomed, please inform us and I will put it in this list:)
Role manager | Author | Description ----|----|---- Default Role Manager (built-in) | node-Casbin | Supports role hierarchy stored in node-Casbin policy
For developers: all role managers must implement the RoleManager interface. Default Role Manager can be used as a reference implementation.
Examples
Model | Model file | Policy file ----|------|---- ACL | basic_model.conf | basic_policy.csv ACL with superuser | basic_model_with_root.conf | basic_policy.csv ACL without users | basic_model_without_users.conf | basic_policy_without_users.csv ACL without resources | basic_model_without_resources.conf | basic_policy_without_resources.csv RBAC | rbac_model.conf | rbac_policy.csv RBAC with resource roles | rbac_model_with_resource_roles.conf | rbac_policy_with_resource_roles.csv RBAC with domains/tenants | rbac_model_with_domains.conf | rbac_policy_with_domains.csv ABAC | abac_model.conf | N/A RESTful | keymatch_model.conf | keymatch_policy.csv Deny-override | rbac_model_with_deny.conf | rbac_policy_with_deny.csv Priority | priority_model.conf | priority_policy.csv
Our adopters
Web frameworks
- Express: Fast, unopinionated, minimalist web framework for node, via plugin: express-authz
- Koa: Expressive middleware for node.js using ES2017 async functions, via plugin: koa-authz
- Egg: Born to build better enterprise frameworks and apps with Node.js & Koa , via plugin: egg-authz
License
This project is licensed under the Apache 2.0 license.
Contact
If you have any issues or feature requests, please contact us. PR is welcomed.
- https://github.com/casbin/node-casbin/issues
- [email protected]
- Tencent QQ group: 546057381



